Apply encryption and security policies automatically for emails and documents that contain sensitive information like social security numbers, payment card information, etc.
Next Generation Solutions
Platform For
SoCs
Deliver enhanced perimeter and enterprise control to your clients by securing their data using post-quantum resistant encryption. Benefit from fine grained policy enforcement and built in compliance meeting the regulatory requirements of many industries and use cases.

The Opportunity
Security Operations Centres (SOC’s) were an inevitable and natural part of the growth of the internet.
From the late 1980’s the SOC’s emerged as early defence systems for the manual monitoring of networks and in particular log files. With a market driven mainly by the military it was not surprising it was going to trip into industry when businesses and organisations realised the power of the Internet and the Web but also realised the threat and vulnerability.
SOC’s never needed a business case for its existence. It was a given. Firmly established by headlines of various major incidents in the 1990s and more commonly viruses (a rampant problem for large corporates), SOC’s become the de-facto insurance policy for peace of mind of the Board and the SME.
Evolution of SOC’s saw a morphing of the term into enhanced managed services (SIEM), followed by game keepers for Advanced Persistent Threats (APT’s) and onto major areas of data compliance and governance assistance for its ever growing demands, from growing market demand.
The further evolution into emerging architecture of Cloud saw yet another stage of evolution – the CloudSOC. Security Orchestration and Response (SOAR) did just that – soar. To be without a SOC offering SOAR was and is unthinkable.
What now for a modern evolutionary SOC? It is clear that there needs to be a bringing together of threat intelligence, SOAR, compliance and business security solutions.
At ScryptX™, we recognised the toolset the modern SOC needed to bring about market driven requirements from it – a natural extension into business security solutions. ScyrptX™ family of products with its parent, ScipherX™ is built around every aspect of the SOC market needs.
Come talk to us….
Build Performant Solutions Leveraging Platform Capabilities
Secure email and Secure data storage are two examples of applications built using ScryptXTM‘s SAIC platform. They
demonstrate the power of the platform and the capabilities available for developing SoCs’ own solutions.
Secure Email
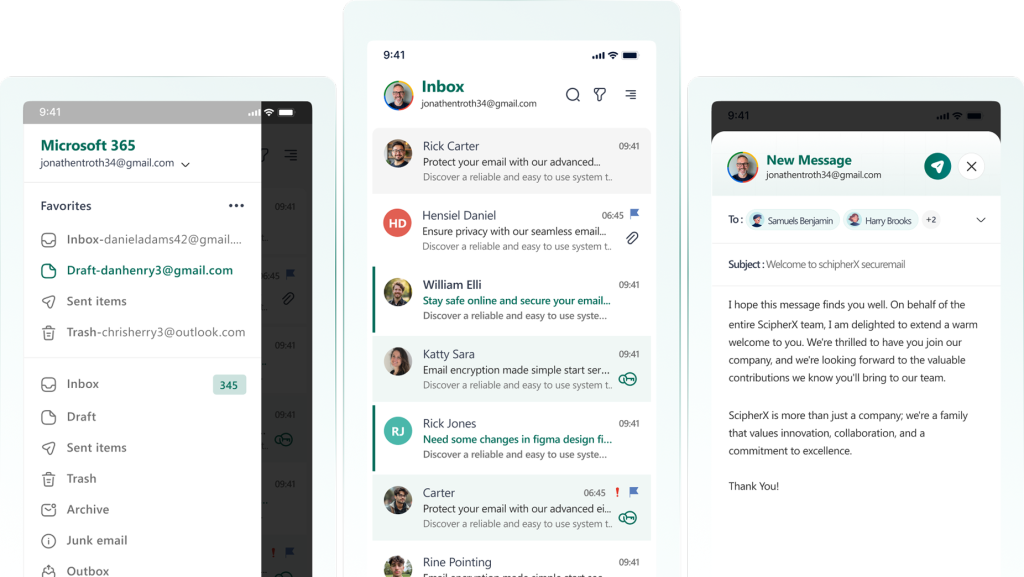
Secure email ensures privacy for the users, encrypting email within the client service (smartphone app, webmail or native email client). The architecture allow users to get up and running quickly and does not require additional training, allowing them to follow normal habits, workflows, and processes.
Secure Data Storage
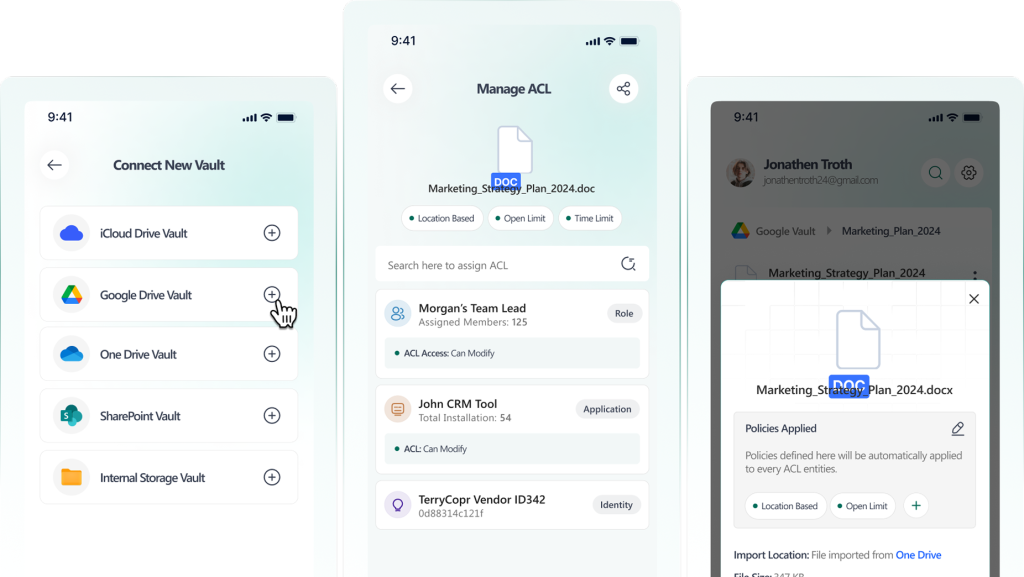
Secure data storage puts the user in control of their data. Files are stored encrypted with the cloud provider, and the keys are stored locally, protecting users and businesses from any security breach with the provider and obfuscating the contents of the files for anyone who is not granted access, including cloud companies.
Create New Applications Rapidly
Benefit from a platform whose architecture and business model were built with SoCs in mind. Leverage standard features like enterprise-grade compliance, organization-wide policies, and advanced controls, to develop and deploy new applications quickly, reducing time to revenue
Enterprise-Grade Compliance
GDPR
Data Sovereignty
Files never leave your chosen region. EU-only hosting option for European data.
CMMC
Defense Contractors
Store CUI with client-side encryption. Meet NIST-approved encryption standards.
Information Security
Meets ISO information security management standards for data protection.
ISO 27001
Healthcare Data
HIPAA-compliant file storage for patient records and medical documents.
HIPAA
Organization-Wide Policies
Establish Maximum Time Limit
Set all emails or documents to expire within a maximum time frame. Users can set shorter time limits, but cannot exceed the maximum.
Mandatory Geofencing
Automatically restrict documents and email with personal information (PII / PPI) to specific geographies
Auto-Apply Policies
Block External Domain
Prevent emails and documents from being sent / shared with specific domains (Competitors, personal accounts, etc).
Advanced Controls
Time Limit Policy
Set a time limit for opening an email or accessing a document; after it expires the email or document becomes inaccessible
Access Count Policy
Limit how many times an email can be opened or a document accessed. Prevent unlimited forwarding and ensure control.
Geofencing Policy
Allows emails and documents to be accessed only from specific locations, denying attempts for elsewhere
Deliver New Recurring Revenue Streams Today
Unlock innovation and new business models to drive scalable and sustainable recurring revenue opportunitieswith healthy margins.
Commercial Approach
- Solutions delivered via a technical, operational and commercial model that, to date, the SOC’s community has never envisaged
- Deliver an immediate increase in recurring revenue with strong margins
- Open-up innovation of other business models for both Enterprises and B2C
Potential applications include:
- Data Security & Governance
- Data Encryption
- Access Control / RBAC
- Dynamic Tag Based Data Control/Management
- Standard + Custom Policies Enforcement
- Cryptography Consulting
- Bespoke System Security Solutions
- IoT Devices Data/Comms Protection
- Key Management Services
Solutions Purpose Built for SoCs
Start the journey of offering enhanced privacy and security to your clients by leveraging a next-generation platform built for SoCs.
Enterprise-grade encryption for email and files,
without leaving your favorite tools.
Company
Products
Legal
© 2026 ScryptXTM. All rights reserved.
